13.02.2026
What is KYC? A Complete Guide to Know Your Customer, Digital Identity and Compliance
KYC, or Know Your Customer, is one of the foundational pillars of the modern digital economy. From banks and fintech platforms to crypto exchanges, marketplaces, telecom operators and crowdfunding platforms, KYC plays a critical role in building trust, ensuring compliance, and protecting users from fraud and financial crime.
KYC, or Know Your Customer, is one of the foundational pillars of the modern digital economy. From banks and fintech platforms to crypto exchanges, marketplaces, telecom operators and crowdfunding platforms, KYC plays a critical role in building trust, ensuring compliance, and protecting users from fraud and financial crime.
At its core, KYC is not just a regulatory obligation, but a system for verifying identity, assessing risk, and establishing digital trust between organizations and their customers. As services move online and onboarding becomes fully remote, KYC has evolved into a complex ecosystem of identity technologies, regulatory frameworks, and automated verification systems.
Today, KYC is no longer limited to document checks in a bank branch. It includes biometric verification, AI-powered fraud detection, real-time risk scoring, and continuous monitoring across digital platforms.
If you want to understand how KYC works, why it matters for digital business, and how modern identity verification systems are transforming compliance, this guide will walk you through every essential concept, step by step.
What does KYC mean?
KYC stands for Know Your Customer. It refers to the legally required process by which organizations verify the identity of their customers and assess their risk profile before providing access to services.
In practical terms, KYC ensures that a person or entity is who they claim to be. It combines identity verification, risk assessment, and compliance checks into a structured process designed to protect financial systems, digital platforms, and users. KYC is not a single action,but an entire framework of procedures, technologies, and controls that operate throughout the entire customer lifecycle.
The Four Pillars of KYC/AML:
- Customer Identification Procedures (CIP): Verifying identity at onboarding.
- Customer Acceptance Policy (CAP): Defining criteria for establishing a relationship.
- Monitoring of Transactions: Continuous surveillance for suspicious activity.
- Risk Management: Assessing and mitigating risks throughout the client lifecycle.
Why KYC exists
KYC was created to protect financial systems and digital services from abuse. As financial crime became more global, digital, and sophisticated, regulators introduced KYC frameworks to ensure that organizations can identify their customers and manage risk effectively.
The core objectives of KYC include preventing:
- Money laundering (AML)
- Terrorist financing (CTF)
- Financial fraud
- Identity theft
- Cybercrime
- Market manipulation
Beyond crime prevention, KYC also supports market stability, consumer protection, and digital trust.
Global regulatory foundations of KYC
KYC is not a local concept. It is built on international regulatory standards that are implemented through national and regional laws.
Global KYC frameworks are shaped by international institutions, regulators, and financial governance bodies. These frameworks define how identity verification, customer due diligence, and risk assessment must be implemented across industries and jurisdictions.
- Financial Action Task Force (FATF): The FATF sets the 40+ Recommendations that act as the global, intergovernmental standard for AML/KYC. These recommendations outline requirements for Customer Due Diligence (CDD), Enhanced Due Diligence (EDD) for high-risk clients, and ongoing monitoring.
- Risk-Based Approach (RBA): Global standards require that institutions take a risk-based approach, assessing the likelihood of illegal activity and applying proportionate, stringent checks (EDD) only where necessary.
Key International and Regional Frameworks
- European Union (EU AMLDs): The EU provides a unified, yet evolving, framework through successive directives (4AMLD, 5AMLD, 6AMLD), emphasizing beneficial ownership and stricter penalties.
- United States (BSA/PATRIOT Act): The Bank Secrecy Act (1970) and the USA PATRIOT Act (2001) require mandatory Customer Identification Programs (CIP), and oversight by the Financial Crimes Enforcement Network (FinCEN).
- Wolfsberg Group Standards: For correspondent banking, the Wolfsberg Group provides industry-specific guidance on KYC to combat financial crime.
- National Regulators: While FATF provides the framework, national bodies (e.g., FCA in the UK, RBI in India) enforce specific, legally binding KYC rules.
What is KYC used for?
KYC is used wherever trust, identity, and risk intersect with digital services. Any organization that provides access to financial, digital, or regulated services must verify who its users are.
Most common industries that rely on KYC include:
- Banking and financial services
- Fintech platforms
- Crypto and Web3 services
- Payment providers
- Insurance companies
- Gambling and gaming platforms
- Telecom operators
- Marketplaces
- Crowdfunding platforms
- Investment services
- Auction houses, galleries
As digital transformation accelerates, KYC is expanding beyond finance into the broader digital economy.
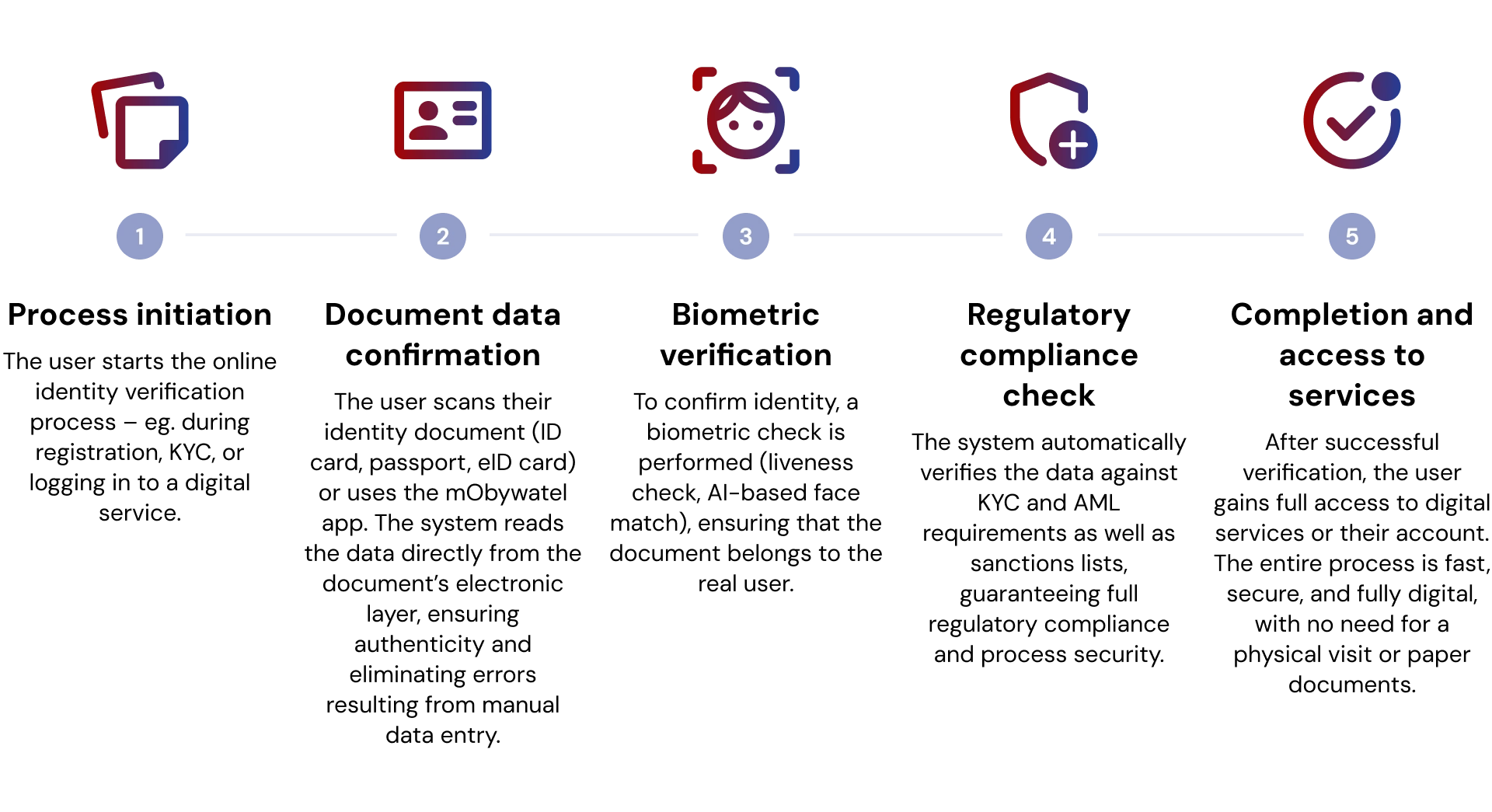
How does the KYC process work?
The KYC process is a structured verification flow that transforms a new user into a verified, trusted customer.
A modern KYC process typically includes:
- User onboarding and data collection
The process begins when a user creates an account and provides basic personal information required for identification, such as name, date of birth, address, and contact details. - Identity data submission
The user submits identity-related data through digital forms or secure interfaces, forming the foundation for verification and compliance checks. - Document verification
Official identity documents (such as passports, ID cards, or driving licenses) are uploaded and automatically validated for authenticity, integrity, and consistency. - Biometric verification
Biometric data, such as facial recognition, is used to match the user’s live image with the photo on their identity document. - Liveness detection
The system verifies that the user is physically present in real time, preventing spoofing attempts using photos, videos, deepfakes, or masks. - Database and registry checks
The user’s data is cross-checked against trusted databases, registries, sanctions lists, and watchlists to confirm identity and regulatory compliance. - Risk assessment and scoring
Risk engines analyze identity data, behavioral signals, and verification results to assign a risk level to the user. - Approval or rejection
Based on verification outcomes and risk scoring, the user is either approved for access or rejected according to compliance policies. - Ongoing monitoring
User activity is continuously monitored to detect anomalies, emerging risks, and suspicious behavior throughout the customer lifecycle.
This process ensures that identity verification is not a one-time event, but a continuous trust model that evolves with user behavior and risk signals.
KYC vs AML vs CDD
Although the terms KYC, AML, and CDD are often used interchangeably, they refer to distinct but interconnected concepts within regulatory compliance. KYC (Know Your Customer) focuses specifically on identity verification and the accurate identification of customers at the point of onboarding.
On the other hand, AML (Anti-Money Laundering) represents the broader regulatory and legal framework designed to prevent financial crime, including money laundering and terrorist financing.
Finally, CDD (Customer Due Diligence) extends beyond initial verification and includes ongoing monitoring, continuous risk profiling, and behavioral analysis throughout the customer relationship. KYC therefore functions as a foundational component of both AML and CDD frameworks, but it does not replace them, but rather supports and enables their effective implementation.
Types of KYC
- Traditional KYC – Traditional KYC involves in-person identity verification using physical documents, typically requiring customers to visit a bank branch, office, or service point for manual verification by staff.
- Digital KYC and eKYC – Digital KYC and eKYC (electronic KYC) refer to remote identity verification conducted online using digital methods such as scanned documents, selfies, and biometric data. These models eliminate the need for physical presence, enabling faster, more accessible, and scalable onboarding.
- Document-free verification – Document-free verification confirms identity through secure access to government-backed digital identity databases, often using biometrics or one-time passwords (OTP) instead of physical documents. This method enables real-time onboarding and is common in countries with centralized digital ID infrastructure.
- Digital identity – Digital identity is the electronic representation of a person’s or organization’s identity, built from verified digital attributes and credentials that enable authentication, verification, and authorization in online environments.
- Video KYC – Video KYC uses a live video call where a compliance officer verifies a customer’s identity and documents in real time, combining human oversight with remote onboarding. In some jurisdictions, video KYC is a regulatory requirement for specific services.
- Automated KYC – Automated KYC uses AI and machine learning algorithms to verify documents, detect fraud, and perform compliance checks instantly without human intervention. It enables scalable, high-volume onboarding with consistent accuracy and speed.
- NFC verification – NFC (Near Field Communication) verification reads secure identity chips embedded in passports or national ID cards to extract and validate user data. This method provides fast, highly secure, and near-impossible-to-spoof identity verification.
Each model reflects different levels of automation, scalability, and technological maturity.
What is eKYC?
eKYC (Electronic Know Your Customer) refers to fully digital identity verification processes that allow organizations to verify customers remotely without any physical interaction. Instead of in-person verification, eKYC uses digital documents, biometric verification, AI-based fraud detection, automated compliance systems, and real-time risk analysis to enable fast, secure, and scalable onboarding across digital platforms.
Risks of poor KYC
Weak or outdated KYC systems expose organizations to serious operational, financial, and regulatory risks. These risks include:
- Regulatory fines – penalties for non-compliance with local and international regulations
- License suspension – loss of authorization to operate in regulated markets
- Fraud losses – direct financial damage caused by identity fraud and account abuse
- Reputational damage – erosion of trust among customers, partners, and regulators
- Cybercrime exposure – increased vulnerability to organized digital crime networks
- Platform abuse – misuse of services for scams, laundering, and illegal activities
- Financial crime facilitation – enabling money laundering and illicit financial flows
Poor KYC doesn’t just create compliance problems. It can weaken the entire business model, undermining trust, stability, and long-term growth.
KYC and data privacy
Modern KYC must operate in full alignment with data protection regulations, ensuring that personal data is collected responsibly, processed lawfully, and handled with the highest security standards. This means limiting data collection to what is truly necessary, managing user consent transparently, applying strong encryption, and storing information securely within compliant infrastructures.
At the same time, privacy must be built into KYC systems from the very beginning through a privacy-by-design approach and continuous regulatory alignment. Only by balancing security, compliance, and privacy can organizations maintain user trust and operate responsibly in the digital economy.
The future of KYC
KYC is evolving far beyond traditional identity checks and fragmented verification processes. It is moving toward intelligent, interoperable, and trust-based identity systems that operate continuously across digital ecosystems. Regulatory frameworks such as eIDAS 2.0 in the European Union are already shaping this transformation by introducing wallet-based digital identities that allow users to securely store, manage, and share verified credentials across services and borders. This model strengthens user control over personal data while enabling fully digital, real-time identity verification without physical interaction.
At the same time, the industry is shifting toward shared compliance infrastructures. Centralized KYC data registries and collaborative identity platforms are emerging as solutions to duplicated verification processes and fragmented compliance models. By enabling secure data sharing between regulated institutions, these systems reduce onboarding friction, accelerate cross-border relationships, and create standardized trust frameworks that operate across jurisdictions.
In parallel, decentralized technologies are redefining how identity data is owned and accessed. Blockchain-based identity models enable users to control encrypted, tokenized credentials while allowing institutions to verify identity without directly storing sensitive personal data. This creates privacy-preserving compliance systems that combine transparency, security, and regulatory traceability with user sovereignty.
The future of KYC is therefore not about verification alone. It is about building digital trust infrastructure, interconnected identity systems that support secure data sharing, regulatory compliance, cross-border interoperability, and user-controlled digital identity at scale.
Conclusion
KYC is no longer just a regulatory requirement. It is the foundation of secure digital services, trusted onboarding, and compliant growth in the digital economy.
From traditional banking to fintech, crypto, marketplaces, and digital platforms, KYC defines how trust is built, verified, and maintained at scale.
As digital identity becomes central to online services, KYC will continue to evolve into a core layer of digital infrastructure, shaping how organizations interact with users in a secure, compliant, and trustworthy way.

Need a custom solution? We’re ready for it.
IDENTT specializes in crafting customized KYC solutions to perfectly match your unique requirements. Get the precise level of verification and compliance you need to enhance security and streamline your onboarding process.